Table of contents
Open Table of contents
- Introduction
- Investigation & Methodology
- 1. Which VPN service was used to send the anonymous email from the .eml file?
- 2. What is the full street address of the petrol station where the missing vehicle was last seen?
- 3. At what time did the suspicious action take place in the route planning system on March 25th, 2026?
- 4. What is the employee ID of the person who sent the anonymous email?
- 5. What is the employee ID of the employee responsible for leaking the shipment details?
- 6. What is the full name of the culprit?
Introduction
Disclaimer: This challenge is inspired by a real cargo theft that occurred in March 2026, in which a shipment of KitKat products was stolen in transit between Italy and Poland.
Background: On 26 March 2026, a refrigerated truck carrying over 400,000 units of KitKat product vanished somewhere between Central Italy and Poland. Nestlé confirmed the theft two days later. The vehicle has not been found. The European Cargo Threat Assessment (ECTA) does not believe this was opportunistic. A shipment of this size, on a contracted route, does not disappear without someone helping it along. An anonymous tip reached a journalist the following evening, and that is where our investigation begins.
The Evidence:
ecta_memo.pdf: The preliminary intelligence assessment.exhibit_a.eml: An anonymous email.exhibit_b.jpg: Photographic evidence.employees.csv&access_log.csv: Subpoenaed from TransEuro Logistics IT.comms_export.txt: Subpoenaed communication logs.
Investigation & Methodology
1. Which VPN service was used to send the anonymous email from the .eml file?
The first step in the investigation was analyzing the anonymous email (exhibit_a.eml). By reviewing the email headers, I managed to extract the originating IP address: 193.32.249.132. Keeping it simple, I ran a direct Google search on this IP, which immediately revealed that it belonged to a commercial VPN provider. This confirmed the informant was trying to hide their real location.
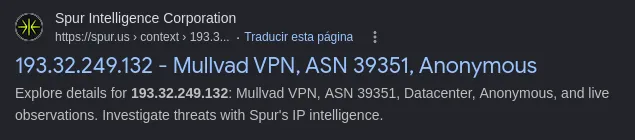
Answer: Mullvad
2. What is the full street address of the petrol station where the missing vehicle was last seen?
My first instinct to find the truck was to look for metadata (EXIF) in the dashcam image (exhibit_b.jpg). Since the metadata had been stripped, I had to apply visual OSINT and cross-reference clues:
- The initial briefing (
ecta_memo.pdf) mentioned the truck was last seen near Hulín. - Upon closer inspection of the photograph, I identified an Orlen petrol station logo.
With these two pieces of data, I opened Google Maps and searched for Orlen petrol stations near Hulín. This led me to the only service station in that area that perfectly matched the visual environment of the photograph.
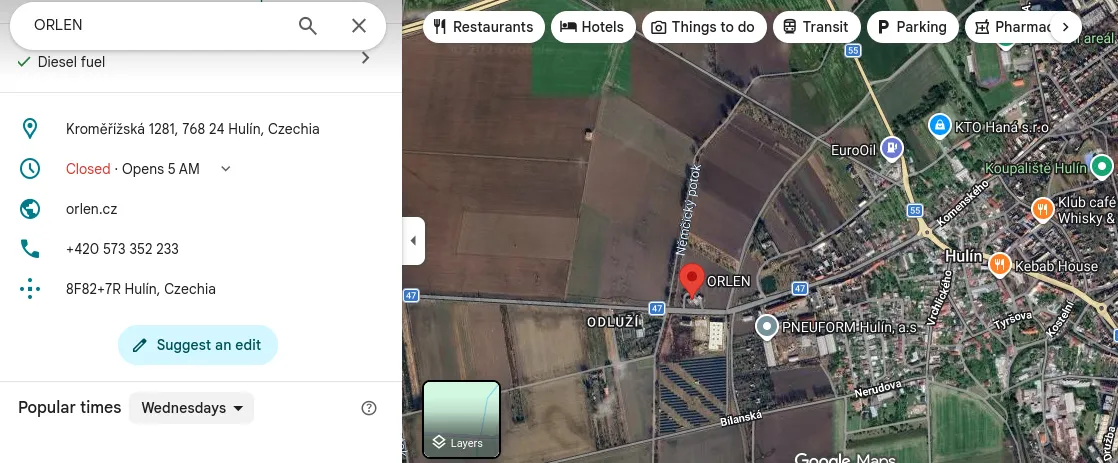
Answer: Kroměřížská 1281, 768 24 Hulín, Czechia
3. At what time did the suspicious action take place in the route planning system on March 25th, 2026?
To find out exactly when the breach occurred, I opened the system logs (access_log.csv). Knowing the theft happened on March 26th, I filtered the events from the previous day (March 25th). While reviewing the activity, I found a critical anomaly: an EXPORT action for the route planning documents was executed at exactly 22:14:09. This was the security breach.
Answer: 22:14:09
4. What is the employee ID of the person who sent the anonymous email?
Continuing to build the timeline in access_log.csv, I looked for who logged into the system right after the 22:14 data extraction. I found that the employee with ID BR-0312 logged in at 23:41.
Cross-referencing this with the employees.csv database, I saw their role was Dispatch Operator and they frequently worked night shifts. This perfectly fits the profile of someone who notices a severe system anomaly outside working hours and, given the internal mistrust expressed in their email (“I do not know who to trust inside the company right now”), decides to leak the situation to the press.
Answer: BR-0312
5. What is the employee ID of the employee responsible for leaking the shipment details?
With the exact time of the data theft confirmed in step 3 (22:14:09), identifying the insider threat was straightforward. The access log undeniably pointed to the user who executed the command on the route documents: employee ID BR-0291.
Answer: BR-0291
6. What is the full name of the culprit?
Since the internal CSV files did not contain the staff’s full names, I had to pivot the investigation. Analyzing the communication logs (comms_export.txt), I detected an external email address (kraliknovak09@gmail.com) attempting to access the route information.
To track down the owner of this email, I avoided typical background check sites (which usually have paywalls) and opted for free OSINT tools. I used Epieos, a tool that scans the digital footprint of an email address. The platform successfully linked that email to a public Google Maps profile; reviewing the reviews written by that account exposed the attacker’s real name.
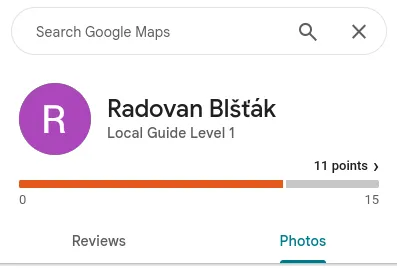
Answer: Radovan Blšťák